The lie: A virtual private network (VPN) connection is very secure. Why it is a lie: VPN encrypts your traffic. But someone could hack into your VPN username and password and access it, and therefore your traffic and all personally indefinable information. Also, your VPN service provider has access to your internet protocol address, URLs you visit, the amount of time you spend connected online, your browsing patterns, data, etc are visible to your provider. A VPN may protect you against your ISP from seeing your traffic, but not from the VPN owner. That is why many governments now use…
Practical application of the Internet of Things
A lot has been said and written about the Internet of Things (IoT) and Big Data (BD), but what is the practical application of these new concepts? So many gadgets and equipment we use daily now have sensors and trackers installed. From the smart television to radios, cars, beds, houses, tables, and heck, everything in between. Millions of cameras installed in so many streets and homes generate lots of data and these are increasingly becoming interlinked. Businesses can apply IoT in many ways: Tracking behavior Decision making powered by sensors Enhanced visibility and situational analysis Optimized resources deployment And processes…
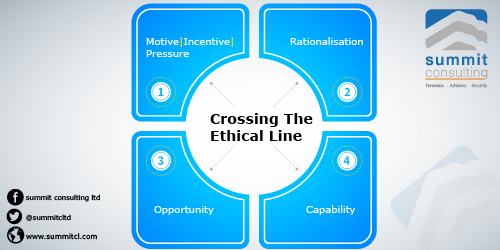
The drivers of cybercrime, excerpts from project frontline
Practical cybersecurity springs from the little decisions we make every day. While almost all data breaches are inspired by malicious intent, their successful execution (almost always) involves seemingly harmless and unintentional actions of insiders within organizations. The drivers of cybercrime include some of the following: i). The well-meaning system administrators who fail to promptly apply patches from application vendors or for some reason just run new scripts on the production environment without the first sandbox testing them. ii). Employees who unsuspectingly yield to social engineering ploys specifically spear-phishing resulting in loss of credentials, money, and corporate data to their adversaries…
Summit Cybersecurity Project Frontline Report 2020 launch
The best and most effective defense against cybersecurity attacks is user awareness. It is against this background that we publish the annual cybersecurity project frontlines report since 2019. During 2019, we undertook 451 assignments spread over 204 clients. Many of these assignments (40%) are outsourced to us, while others are directly handled, and some reported by our associates and affiliates spread regionally. We are aware of our responsibility to keep client information confidential at all times, something we guard jealously, and this report does not in any way disclose any specific client information. Cybersecurity awareness is the best defensive strategy…
ICPAU webinar on cybersecurity and IT risks: are you secure online?
In mid-June 2020, someone called requesting my help recover his personal Gmail address that had been hacked. You could hear his desperate voice on the other end of the call. He explained that since the coronavirus pandemic, board members decided to be sending all official documents and board packs to several preferred emails of each board member. “Can you recover my Gmail password and get it from the hackers. I am afraid they are going to see all the board papers and details, which will be catastrophic,” he said. Any victim of cybercrime needs their service restored as soon as…
Australia reports a massive cyber attack by a state actor
Canberra, 19th June 2020: A massive cyber-attack is spreading across the world, as it causes chaos in its wake. It has been reported in global online media that “On Friday, a massive wave of cyber-attacks swept across 99 countries, with cyber-security experts claiming it could be the biggest attack of its kind ever recorded.” The Australian media reported the following: “Prime Minister Malcolm Turnbull insisted that even if we are targeted, the government is prepared. We are continuing to monitor the situation closely and stand ready to deal with any cyber-security threat to Australia’s critical infrastructure,” he said through a…