Every board loves to talk about “digitisation” and “firewalls.” But here’s the truth: the easiest way to hack a ministry, bank, or NGO is not through code, it’s through ghosts on payroll. When HR fraud meets weak IT, cybercrime becomes institutionalized. That’s why I designed the Boardroom Payroll Integrity Tool, a no-excuses dashboard for leaders who want to know if their payroll is a fortress or a fraud pipeline. Ask yourself: a) Can you prove every person on payroll exists? b) Who controls the power to add or remove names? c) Are payroll anomalies linked to IT audit trails—or are…
Death is the greatest democracy
On Saturday, I drove over 250km to Kagadi. Not for a wedding. Not for a political rally. But for the burial of a man who lived 100 years and shook the very ground he walked on. By the look of things, the entire district of Kagadi and Hoima closed shop. Over 5,000 people. Ranked and unranked. Big men and nobodies. They all showed up. Not for a concert. Not for money. But to bury a man. That is how powerful he was in life. And yet, he still bowed. That is the irony. Death doesn’t respect influence. It doesn’t care…
Would your team recognize a phishing attempt today in the organization?
Three years ago, I worked with an organization that prided itself on having “world-class” IT controls. Firewalls, intrusion detection, antivirus subscriptions, the full package. During a strategy execution session, I asked the CEO one simple question: Would your staff recognize a phishing attempt if it landed in their inbox today? He smiled and said, “Of course. We train them every year.” To test the assumption, we ran a controlled phishing simulation. Within 24 hours, 41% of staff had clicked the malicious link. Even worse, several forwarded it internally, magnifying the risk. The breach did not start with servers; it started…
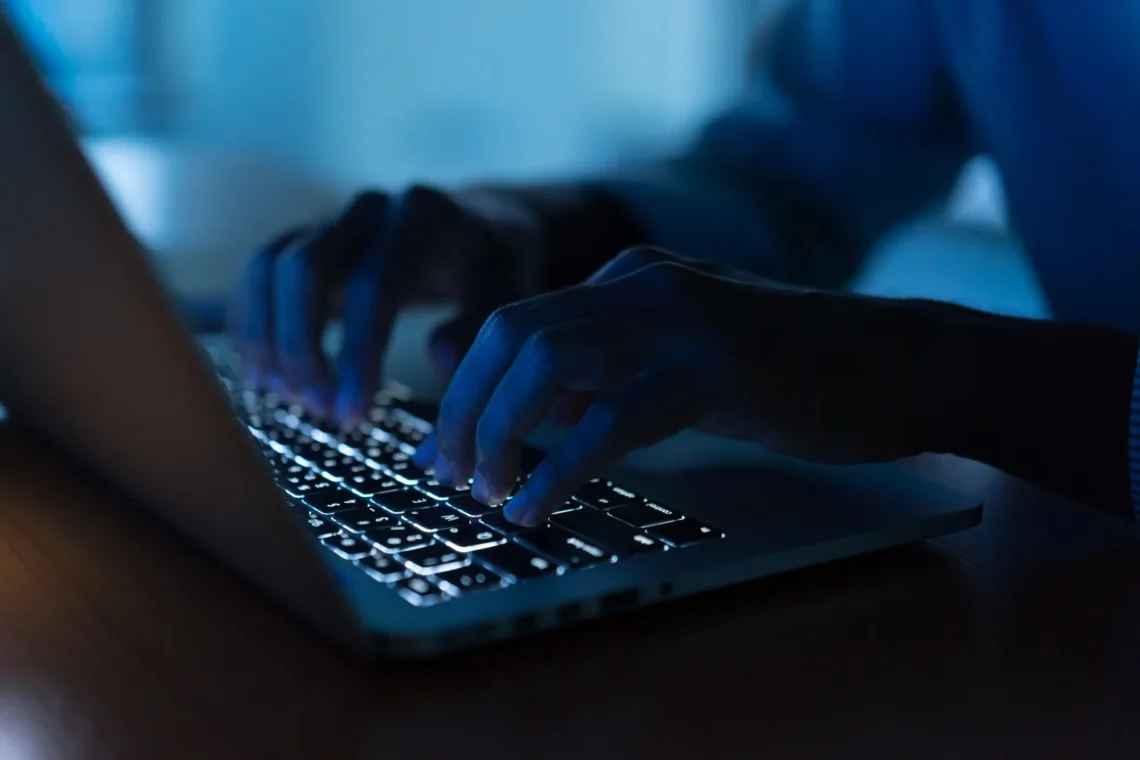
How hackers use curiosity against you
It started with a link. One click. That’s all it took. On a cool Friday morning in April 2025, a procurement officer at a leading Ugandan NGO, let’s call her Susan, received a WhatsApp message from an unknown number. The message read: “Hi Susan, I saw this on Twitter about your organization. Thought you should see it.” (link attached) The link preview showed the NGO’s logo with the caption, “Shocking scandal involving NGO procurement manager leaks online.” Her heart raced. Susan clicked. Nothing loaded. “Maybe it’s my MTN data,” she thought. She brushed it off. But unknown to her, that…
The hidden costs of ignoring cybersecurity in an organization
It never starts with a bang. Cyber fraud does not arrive at your doorstep with sirens. It whispers in the background. A delayed payroll here, a customer complaint there, a donor asking awkward questions about leaked contracts. By the time executives pay attention, the damage is entrenched. Cyber risk is a slow bleed, and the organizations that dismiss it as an IT issue end up paying the highest, most invisible bills. The illusion of savings Boards and their executive management love to postpone “non-core” investments. Cybersecurity tops that list. “We’ve never been hacked. Let’s deal with it next year.” That…
Do banks use dormant accounts for fraud?
Why do banks demand a board resolution to reactivate an account they themselves marked “dormant” simply because you did not transact? Why design hurdles that punish a customer for inactivity instead of rewarding them for loyalty? I see this as a paradox of modern banking. Banks preach financial inclusion while erecting barriers to access. They claim to protect you from fraud, yet what they protect is their bureaucracy. A dormant account is not a risk; it is an untapped opportunity. In modern banking, smart banks treat dormancy as a trigger for engagement, not punishment. They call, they nudge, and they…